Information Management Survey Report
Astral Consulting Services and Swinburne University of Technology are pleased to present the findings from an Information Management online survey conducted earlier this year. The survey was carried out across four key areas: - Information Governance & Security,-...
INDUSTRY BRIEFING: Microsoft 365 Records Management – Opportunities and Challenges
Compliance, risk management, and legal requirements are not the only drivers for corporate records management. When managed effectively, business records generate significant business value by enabling the capture and re-use of intellectual property and corporate...
INDUSTRY BRIEFING: Dispelling Common Myths about Information Governance
Continuing our series of articles on information security, we dispel some common misconceptions about emerging trends in information governance. Myth 1: Cloud computing takes care of information governance. Public cloud services generally offer highly available and...
INDUSTRY BRIEFING: Emerging Trends in Information Governance
The role of information governance is changing rapidly alongside technological developments. As the volume and speed of information and data transactions increase, risks emerging from data breaches, and the importance that businesses place on the governance of...
INDUSTRY BRIEFING: What’s New in Information Governance?
Technology plays an important part in enabling information security and the management of personally identifiable information (PII). However, recognising that human factors are just as important, Astral’s approach to PII risk management is driven by information...
INDUSTRY BRIEFING: Privacy by Design – Increasing PII Security
Cyber-attacks and data breaches are rapidly increasing in sophistication, with immense ramifications for companies and their customers. Australian companies are under greater obligation than ever to manage their customers’ Personally Identifiable Information...
Information Management Survey Report
Astral Consulting Services and Swinburne University of Technology are pleased to present the findings from an Information Management online survey conducted earlier this year. The survey was carried out across four key areas: - Information Governance & Security,-...
INDUSTRY BRIEFING: Information Governance strengthens Data Security. Is your Organisation Ready?
The Optus and Medibank data breaches illustrate the importance of Information Governance for ensuring businesses have the latest security standards, protocols and organisational discipline to effectively respond to the latest wave of international cyber-attacks. The...
Value Case 1: Global Oil & Gas Exploration Organisation
Continue reading of some examples where Astral has provided value to Mining organisations, through Enterprise Information Management solutions by clicking on the links below. Links Astral Use Case - EIM Value - Mining Sector - Astral Value Case 2: Global Mining...
Value Case 2: Global Mining Organisation
Continue reading of some examples where Astral has provided value to Mining organisations, through Enterprise Information Management solutions by clicking on the links below. Links Astral Use Case - EIM Value - Mining Sector - Astral Value Case 1: Global Oil & Gas...
Value Case 3: Global Mining Services Organisation
Continue reading of some examples where Astral has provided value to Mining organisations, through Enterprise Information Management solutions by clicking on the links below. Links Astral Use Case - EIM Value - Mining Sector - Astral Value Case 1: Global Oil & Gas...
Value Case 4: Global Mining Organisation
Continue reading of some examples where Astral has provided value to Mining organisations, through Enterprise Information Management solutions by clicking on the links below. Links Astral Use Case - EIM Value - Mining Sector - Astral Value Case 1: Global Oil & Gas...
Astral Use Case – EIMaaS – Energy Organisation
Enterprise Information Management as a Service (EIMaaS) Customer Success Story – Energy Organisation The Business Problem Our customer is an energy company that operates in Australasia and North America, who had been using an EIM as a service provider for a...
Astral Use Case – IM Strategy – Financial Organisation
Information Management Strategy Customer Success Story – Financial Organisation The Business Problem This Astral client is a large financial organisation that operates Australia-wide. The organisation set the strategic direction to consolidate all IM...
Astral Use Case – IM Strategy – Federal Agency
Information Management Strategy Customer Success Story – RM Solution Assessment The Business Problem This Astral client is an Australian federal agency that has offices in all Australian states and territories, who engaged Astral to perform an...
Astral Use Case – IM Strategy – Water Utility Company
Information Management Strategy Customer Success Story – Water Utility The Business Problem This Astral client is a Victorian-based water utility who requested the preparation of an Enterprise Content Management (ECM) strategy and roadmap to address the...
Astral Use Case – IM Strategy – Mining Organisation
Information Management Strategy & Roadmap Customer Success Story – Mining Organisation The Business Problem This Astral client is head officed in Melbourne, Australia, with global operating sites. They currently manage their unstructured information...
Astral Use Case – EIMaaS – Global Oil Exploration Company
PROFILED ORGANISATION Our client is a global energy company that has operational assets of both LNG and Oil delivering high value energy that meets the needs of society with a mix of greenfield and brownfield assets. EIM is leveraged to drive the embedded value of...
Astral Use Case – EIMaaS – Mining Services
Enterprise Information Management as a Service (EIMaaS) Customer Success Story – Mining Service The Business Problem This customer provides services to help mobilise the vital resources required by mining companies globally. The organisation is head...
Astral Use Case – EIM Value – Mining Sector
Delivering Enterprise Asset Value - Mining Sector Astral work together with our clients to put in place an information management and governance building blocks framework. Setting a foundation for driving value from the client’s enterprise information management...
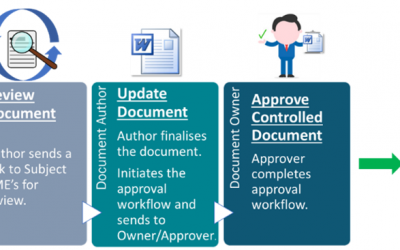
Controlled Document Solution Implementation
The Business Problem This customer is head officed in Melbourne, with global operations across more than 100 countries, providing services to help mobilise the vital resources required by mining companies globally. The organisation required the implementation of a...
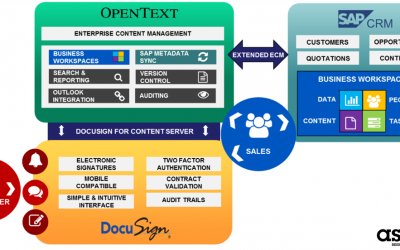
ASX 100 Retail Digital Contracts Solution
The Business Problem The existing business process to contract a new or existing customer was very manual. On receipt of a contract the customer must print, sign, initial each page, scan and send back their contract(s) to accept the service provider energy offer. The...
CASE STUDY: Information Governance – Professional Services
Client Our client is a national peak body for a professional services association comprising 170,000 individual members. The organisation is committed to promoting professional development and advocacy for its industry. Astral was engaged to ensure its members'...
CASE STUDY: Global Policy Framework for Asset-Intensive Business
Client Our client is a global producer, manufacturer and re-seller of chemical products. They required a robust global framework to support effective records and information governance across their operations in multiple geographical locations. The framework needed to...